Live streams from various cable and broadcast networks we observed for several months generally had IP addresses that originate from Europe, irrespective of whether the source channel is an American, Canadian, or European service. Recently, the European source used by many live streaming aggregators was blocked or shut down, and the streams re-appeared from a stateside IP address in less than 24 hours. Streams of unauthorized recorded content are available from many different sources, usually including Eastern Europe, the Middle East, and various island nations.
The unauthorized recordings may have been received from a programming service, authorized streaming service, DVD, off-air, or even shot with a camera in a movie theater. Many recorded TV shows and movies carry the logo bugs of the service that transmitted them. Of course, an American live stream is not really originating in Europe. Someone in the US is receiving the stream and sending it to Europe for re-streaming. This can be confirmed from the locally inserted commercials, set-top box artifacts, or emergency alert broadcasts.
Who is doing it, and is it legal?
In a social media forum, I came across a person acting as a player in the cottage industry described above. He was responding to complaints about their cable service. He offered people an alternative: Buy a streaming player from a local store or Amazon, send it to him, pay a little cash, and get back something that can get all of your TV from before and more. You can then disconnect your cable video service and save lots of money. Of course, some were a bit leery about the legality of doing such a thing and posted their concerns. He would respond that lawyers, policemen, fire fighters, and other upstanding community members were customers, and that the current law does not define end-user streaming as illegal. He is doing dozens of these conversions every month, and has many happy “customers.”
While it may be true that under current law end customers face a limited risk of committing a crime, the subscription seller and software loader is almost certainly doing so under the “Inducement Rule,” which was used in the Napster days to go after those selling means to violate copyright law. The inducement rule basically states that one promoting or enabling copyright violation is committing such a violation.
What about the streaming sites? Obviously, having copyrighted material on a server and broadcasting it without authorization is a direct violation. Copyright violations contained within the material advertising unauthorized streams may be used as indications of wider violations of copyright to assist in legal challenges against these services.
It is clear that we need better legal and technological tools to address this problem.
What to do?
With the problem defined, what can be done to combat this threat?
Legislate/Litigate. At a minimum, the existing protections provided by the DMCA must be extended to specifically cover unauthorized streaming. This type of change has already happened in Europe by court interpretation. New legislation at the national level should make it clear that stealing is stealing, and receiving stolen goods (or TV services) is a crime.
Those providing any of the unauthorized parts of the ecosystem could be challenged in civil court. Once identified, a streaming server provider or box modifier could be sued for loss of revenue or other damages. End users could similarly be targeted.
Public Relations. Faced with losses from illegal music downloading, the music industry ultimately reached a model of distribution based on inexpensive authorized downloads combined with free or inexpensive authorized streaming subscription sources. 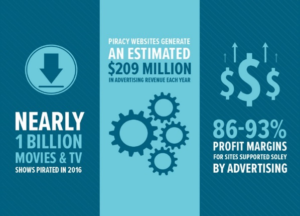 They also waged a public relations campaign designed to make it clear what was legal and what was not. Efforts started by the Alliance For Creativity, for example, help to educate the public about the ultimate costs of unauthorized streaming. Internal Industry efforts are also underway at NCTA. New campaigns could be undertaken to emphasize the risks to the end user, outlined below, and to help the public determine the difference between a legitimate streaming provider and an unauthorized one.
They also waged a public relations campaign designed to make it clear what was legal and what was not. Efforts started by the Alliance For Creativity, for example, help to educate the public about the ultimate costs of unauthorized streaming. Internal Industry efforts are also underway at NCTA. New campaigns could be undertaken to emphasize the risks to the end user, outlined below, and to help the public determine the difference between a legitimate streaming provider and an unauthorized one.
The home user of unauthorized streaming services faces several risks:
Legal Action. When effective laws can be enforced, the user risks criminal or civil action. They might be traced technologically or from a subscriber list of an unauthorized streaming service to which they subscribed.
Downloading of malware could jeopardize the security of their home network and all devices connected to it. The software required to play unauthorized streams and catalog the unauthorized products can have hidden malicious programs embedded within them. Software tools required to install the player software products to a streaming device from a PC are even more at risk. Malware could range from password-stealing trojans to ransomware and spam generators. With the software installed on a device behind a user’s router, other devices in the home network can be targeted.
Unreliable service as streams and their providers come and go. As unauthorized stream sources are taken down, the user will lose service. We observed that sources may not operate on a regular basis even under normal circumstances. Once a source is lost, the user may need to take direct action to find a new way to obtain a replacement, including loading a new player or specifying new access credentials. As stated previously, the end user may be completely unaware that their choice of streaming service provider is selling unauthorized streams.
Technology
On the player front, one could mandate hardware protection (as with the HDMI interface copy protection scheme) but it would take years to end up in the products, and unprotected products or hacks would likely still be available.
Why not go after the illegal streaming servers? Internet Service Providers have the means to detect and determine the IP address source of illegal streams, once they have been identified as such. These IP addresses could be traced back to their ISP and ultimately to the source server via the same means used to locate filesharing servers. This would mean that the content owners and ISPs would have to cooperate, or at least respond to court ordered requests, as they do with filesharing today.
Watermarking technology provides a good basis on which to build a means to identify streams. If all legitimate streams are uniquely marked at as many points in the distribution chain as possible, a peek into the watermark in the unauthorized stream could point to the source or at least the video service provider involved. The same techniques could be used to tag VOD streams as their authorized originals are transferred into an unauthorized streaming source library.
Encryption. If the stream user employs a VPN, the source address of the streaming server is encapsulated in the encrypted stream. If the user’s ISP blocks that address, the stream will still go through as an encrypted flow from the source IP of the VPN service providing the encryption to the user rather than the streaming server itself. For this reason, the only truly effective means to stopping the stream would have to be employed at the ISP of the server rather than just the user. Blocking streams involves Network Neutrality considerations. Most Network Neutrality laws and regulations allow for blocking “illegal” transmissions – – all the more reason to make certain that laws define unauthorized streams as illegal.
Summary
The plethora of streaming hardware, coupled with widespread availability of unauthorized sources of aggregation and streaming content is a growing phenomenon which, if unchecked, will grow larger and larger. Streaming video from unauthorized sources represents a challenge to the very existence of the television industry. Programmers and Service Providers must come together to step up to the challenge. Only Programmers can help to make their authorized streams more identifiable, and only Service Providers can trace those streams to their unauthorized sources and hopefully stop them. The actions we, as an industry, take now will help determine if television’s new Golden Age turns out to be “Fool’s Gold”.
Jack Burton, Broadband Success Partners


